Published on
We are currently in an application security dilemma that stems from growing security concerns, pressure on development teams, and a lack of structured security training.
Let's take a look at some stats:
- Recent studies show 210% new vulnerabilities per year in the National Vulnerability Database
- 92% of developers feel pressure to release code to market faster
- Top 50 US university coding programs currently don't require their students to take secure coding courses
This dilemma is affecting organizations and is why application security has not improved over the last decade.
Security Journey provides engaging and effective AppSec training to developers and all members of the SDLC. With over 450 customers, from large enterprises to small startups, our team is always asked, "Can I show an ROI on my AppSec training investment?"
In this article, we will review the business impact of an application security risk, the cost of AppSec training, and show how you can calculate the ROI of AppSec training.
The Impact of an Application Security Risk
We outlined the security dilemma above, but what does this mean for your organization?
Let's consider that almost 95% of data breaches last year were on web apps, and 56% of the biggest incidents in the last 5 years tie back to web app security issues. It often takes more than eight months to find a web app exploit, which means that your business and your customers can be exposed to attackers for an extended period of time.
Attacks on web apps have cost over $7.6 billion, representing 42% of all financial losses from attacks.
Continuing the current status quo of pressured development teams with little to no security training working in an ever-growing field of new vulnerabilities can severely impact your business through financial losses, damaged reputation, and liabilities.
Organizations are paying attention to the impact of an application security risk and taking steps to protect themselves and their customers. For example, 99% of organizations have security awareness training programs, with short overview sessions such as OWASP 10. While this is an important step for organizations, this is just a starting point. Less than half of organizations are training developers specifically on secure coding, therefore finding vulnerabilities reactively rather than coding securely from the start.
How Much Does Application Security Training Cost?
Application Security Training focuses on educating developers (and others in the SDLC) on best practices to create safer apps and the consequences of common threats and vulnerabilities.
When looking at how your organization handles threats, there are two approaches:
- Remediating vulnerabilities after production
- Preventing vulnerabilities during production
Each of these approaches has its own cost; let's take a look at the calculations.
Cost to Remediate Vulnerabilities
It often takes up to 7 hours for a vulnerability to be detected, prioritized, and remediated – making your application a sitting duck. When your team does learn of a vulnerability, you need to act quickly to remediate the problem.
Studies show that the average time to detect, prioritize, and remediate one vulnerability is 7 hours.
Let's look at the calculations:
- A team is faced with 5,000 vulnerabilities
- They fix at least 30% of the vulnerabilities = 1,500 vulnerabilities to fix
- 1,500 vulnerabilities @ 7 hours each = 10,500 hours of developer work
- 10,500 hours of developer work @ $72/ hour* = $757,215
The total average cost to remediate vulnerabilities is $757,215 annually.
* This assumes a $150k salary.
Cost of AppSec Training Programs
While it may take months to remediate a vulnerability, you would probably want to avoid having your team redo completed work – this means writing secure code from the start.
There are many ways to train application security at your organization, from in-house program development to third-party platforms like Security Journey's AppSec Training, that are created by industry professionals.
When looking at the cost of an application security platform, you can see a couple of variables:
- Cost of the education platform license – often per user on a monthly or yearly basis
- Cost of the time for developers to complete the training (hourly pay) – often reoccurring yearly
Let's look at the calculations for a team of 100 developers using average pricing quotes:
- Average cost of the education platform = $36,000
- Time to complete training - 12 hours per year @ $72/hour = $86,400
The total average cost to train 100 developers on application security is $122,400 annually.
What is the ROI on Application Security Training?
Now it's time to answer the key question: What Is The ROI On Application Security Training?
Taking our calculations from above:
- The total average cost to remediate vulnerabilities is $757,215 annually.
- The total average cost to train 100 developers on application security is $122,400 annually.
Now let's do the calculation for your ROI On Application Security Training:
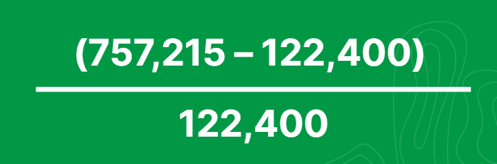
This calculation shows that AppSec Education has a 5x ROI, assuming you can prevent the same 30% of vulnerabilities you would want to remediate each year.
So not only are you preventing vulnerabilities and reducing exposure – your AppSec Training Program is paying for itself. This calculation doesn't account for the organization's risk reduction by preventing vulnerabilities, reducing the overall attack surface, and the value of protecting your and your customer's data – which only add to the value of a solid AppSec Training Program.
Do the Numbers Add Up?
In this article, we reviewed the business impact of an application security risk, the cost of vulnerability remediation and prevention, and how you can calculate the ROI of an AppSec training program.
Are you ready to calculate the ROI for AppSec Training at your organization? You can contact our team today to learn more or jump into our portal and try our AppSec training for yourself.


