Try Security Journey's Secure Coding Training
Security Journey offers diverse training content in easy-to-digest lessons that help educate developers and everyone in the SDLC to shift left and build safer applications.
Watch Our 3-Minute Product Overview Below
A Programmatic Approach to AppSec Education
Our multi-year, customizable training programs upskill developers and educate all roles in the development process to deliver measurable results with our AppSec Education Platform.
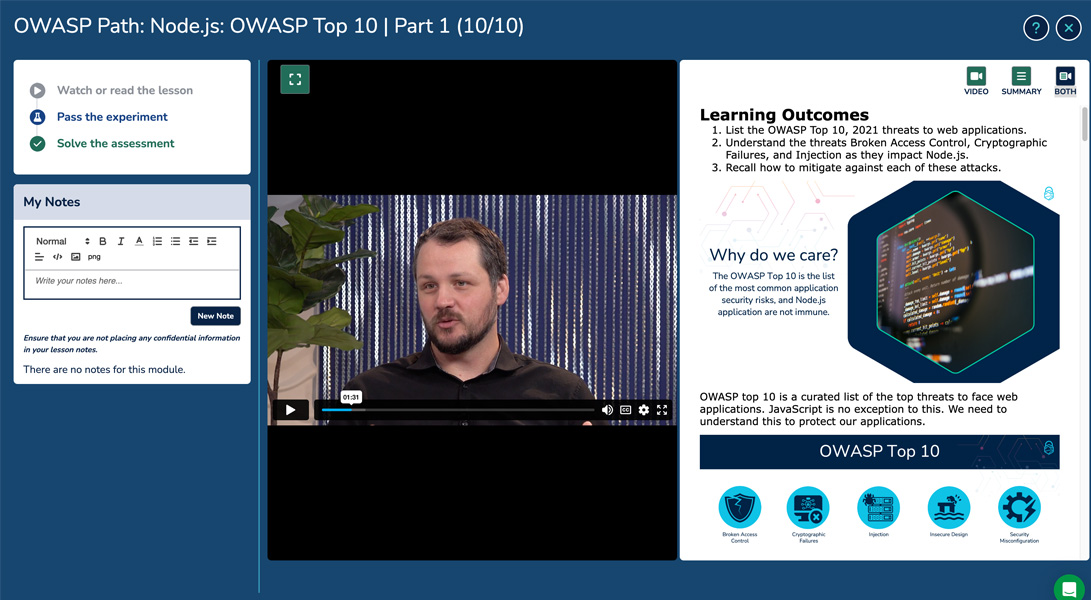
Security Journey's wide variety of content covers everything from foundational concepts in video-based security conversations to engaging break-and-fix exercises for developers.
Learners report an average of 34% knowledge gain, with some learners improving their knowledge by as much as 85%.
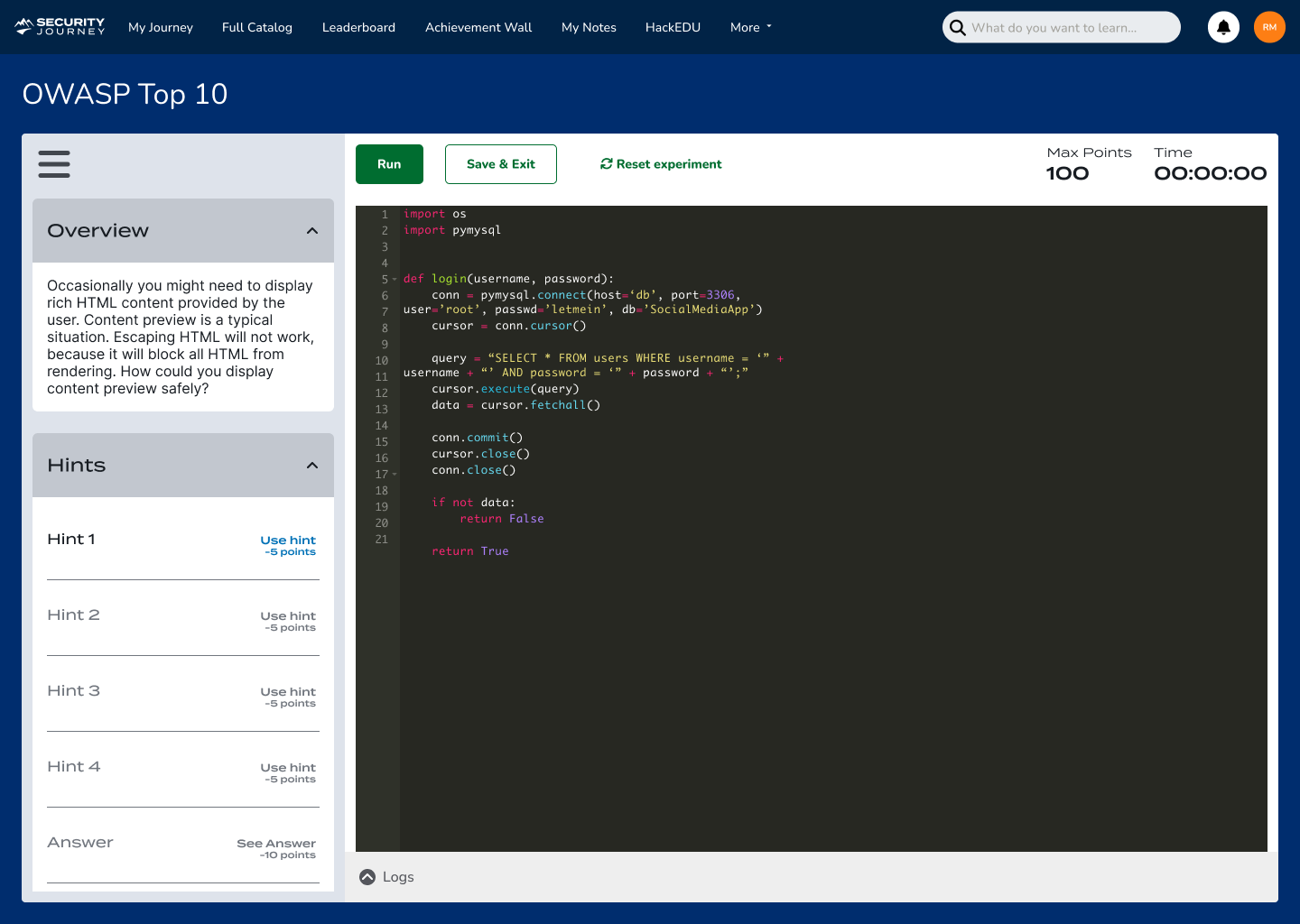
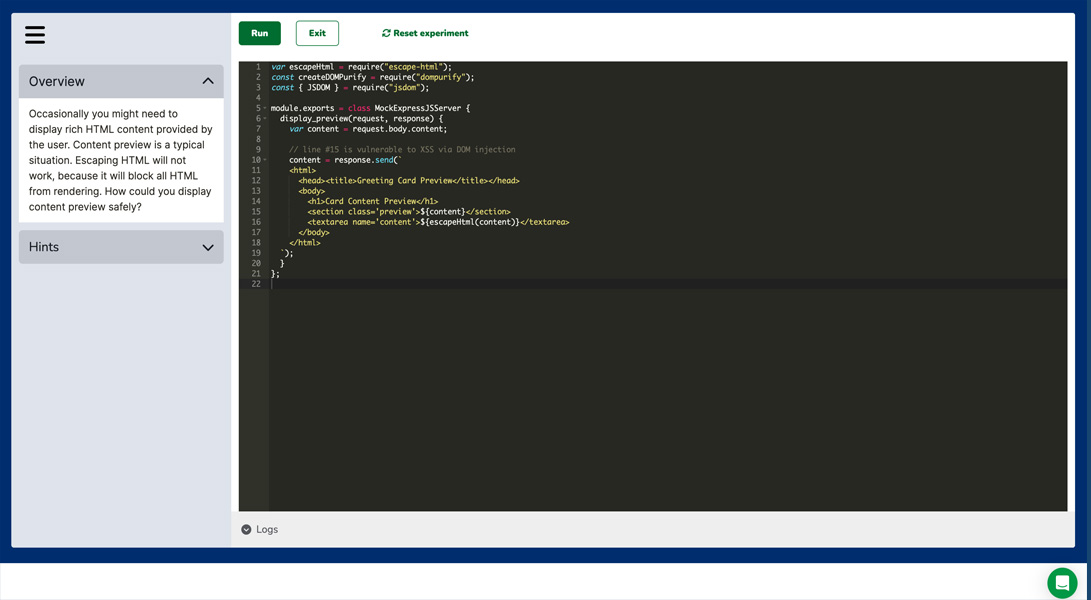
Hands-On Lessons
Give your team HackEDU immersive learning that gives them a space to practice breaking and fixing code.
Getting Started With Hands-On Secure Code Training Today
The Security Journey AppSec Education Platform is a top-rated solution that brings you:
- A proven educational program that teaches secure coding best practices through engaging content
- Tournaments that drive engagement at all experience levels
- Customizable interface to match your company culture
- Easy to build and deploy training plans